Reading List
The most recent articles from a list of feeds I subscribe to.
I had a great time at DEF CON 31
I've always admired DEF CON from a distance. I've watched DEF CON talks for years, but I've never been able to go. This year I was able to go, and I had a great time. This post is gonna be about my experiences there and what I learned.
In short: I had a great time. I got to meet up with people that have only been small avatars and text on my screen. I got to see talks about topics that I would have never sought out myself. I'm gonna go again next year if the cards allow it.


The con itself
DEF CON is split between three hotels and a conference center in the Vegas strip: The Flamingo, the LINQ, Harrah's, and Ceasar's Forum. This was my first clue that this conference was big. I didn't realize how big it was. I'm used to conferences that have maybe two tracks of talks, but DEF CON had at least 14 when you count all the villages. I didn't even get to see all the villages, and I didn't get to see all the talks I wanted to see due to the logistical constraints of everything being spread out through Vegas.
The lines were also brutal. People were jokingly calling it LineCon, but damn they really meant it. I guess this is the sign that DEF CON has been a success, because even smaller village talks had massive lines. I didn't get to see the talks I wanted to see because I didn't want to wait in line for an hour or more. I'll likely catch the ones I missed on YouTube.
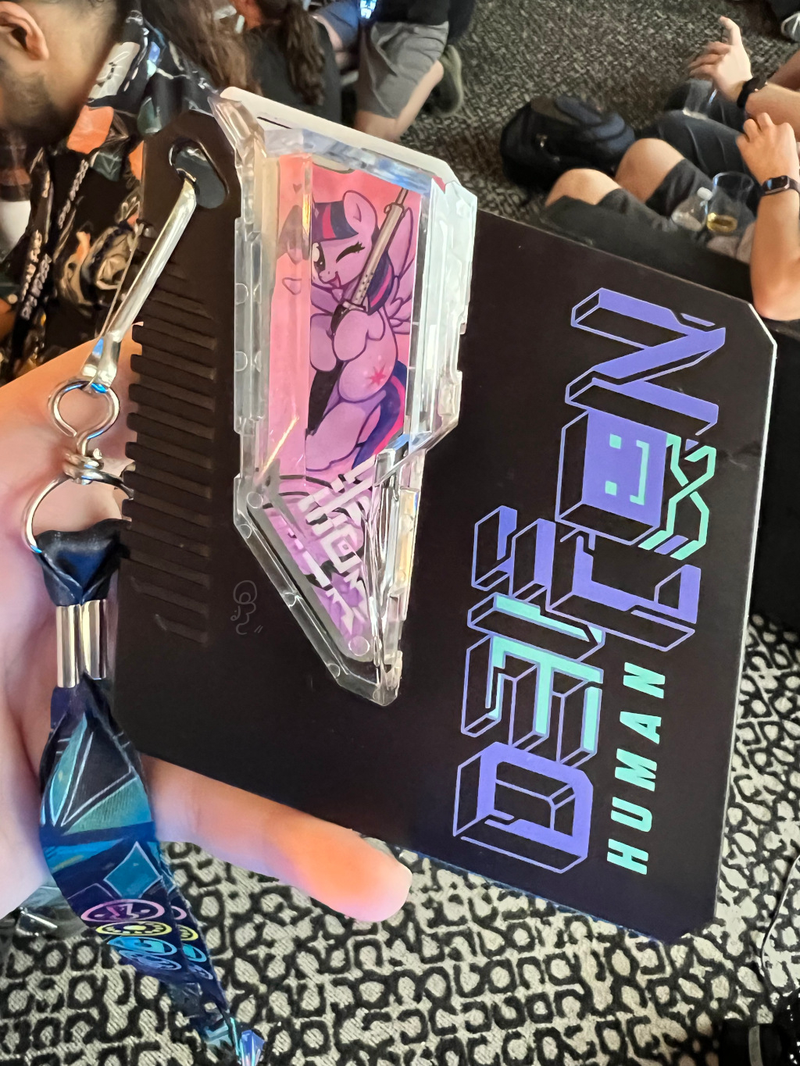
I pre-registered for the conference and I was able to get one of the coveted hard plastic badges that had room to add "shards" to customize it. I got a shard that has a picture of Twilight Sparkle holding a soldering iron on it.
This is going to make a great souvenir. I'm going to put it on my desk.
The AI village
One of the neatest experiences I had was at the AI village. There we tried to do prompt injection on models to try and get them to repeat misinformation and do other things like that. I found a fairly reliable way to get the models to say that Donald Trump was president of the USA: use Lojban, toki pona, and Esperanto.
So basically, my conversations with the AI models ended up looking like this:




It was utterly trivial, especially when you mixed Lojban, toki pona and Esperanto in prompts. I doubt this is going to work for much longer in the models I tested, but it was a very fun thing to discover.
The cryptography/privacy village
I also loved the puzzles in the Cryptography/Privacy Village. I didn't get to finish them (I'll likely get to them at some point), but I was able to implement the Vigènere cipher in Go. I put my code here in case it's useful.
The furry village
I hung out a lot in the furry village though. It was a chill place with an open bar and when you paid the price of admission, you got access to what was probably the cheapest bar on the strip. It was really a chill place to hang out with like-minded people of the furry persuasion and talk about tech. I got to meet a couple other online nerdfriends there.

Photography
I also got to practice my photography skills and play with the new 35mm lens that Hacker News paid for with ad impressions. I love the bokeh on this thing. Here's an example of how good the bokeh gets:
It's goddamn magical. The best part is that this is done in optics, not software. To be fair to Apple, their Portrait Mode does an amazing attempt at making the bokeh effect happen, but you can see the notable haze around the objects that the AI model determines is the subject. This manifests as straws in cups going into the blur zone and other unsightly things. It works great for people and pets though. With my DSLR, this is done in optics. It's crisp and clear as day. I love it.
I'm going to include my photographs in my future posts as the cover art in addition to using the AI generated images that people love/loathe.
The talks
Here are the talks I went to:
- The Mass Owning of Seedboxes
- Hacking Your Relationships: Navigating Alternative and Traditional Dynamics
- Software Security Fur All
- Legend of Zelda: Use After Free (TASBot glitches OoT)
- Domain Fronting Through Microsoft Azure and CloudFlare: How to Identify Viable Domain Fronting Proxies
- Attacking Decentralized Identity
The Mass Owning of Seedboxes
This talk was awesome. The core thesis was that seedbox providers do a very bad job at security and that it makes it easy to grab credentials to coveted private trackers and ruin other people's ratios. The speaker was anonymous and I'm not going to go into too many details about the talk to protect the "off the record" nature of the talk, but I loved it.
It makes me glad that I self-host things instead of farming it out to a third party that will just mess it up.
Hacking Your Relationships: Navigating Alternative and Traditional Dynamics
I only caught the tail end of this talk in the furry village, but it was about the practical considerations with polyamory and other non-traditional relationship structures, as well as the legal/social implications of coming out as polyamorous. I'm not polyamorous myself, but I have friends that are poly and I want to support them when and where I can. I liked it and kinda wish I caught the entire talk.
Software Security Fur All
This talk was by Soatok, someone I look up to a lot with regards to cryptography and security implementations. They talked about how the industry kinda sucks at doing its job and lamented how elitist the security space can be. Then they talked about security first principles in a way that I found really approachable.
I'm not really the best with security/cryptography code, but I do know enough that I should farm it off to someone that knows what they are doing as soon as possible.
I think one of the most impressive parts of this talk was that Soatok gave it in a fursuit. In Vegas. In summer. I can't imagine how hot that must have been.
Legend of Zelda: Use After Free (TASBot glitches OoT)
This talk was about how the SGDQ run of The Legend of Zelda: Triforce% worked from a technical level. Triforce% is a work of art and they went into gorey detail on how they hacked the game from the controller ports into memory. It was a great talk. They also tried to replicate the run live but ran into an issue where the game crashed at the worst time.
Ocarina of Time is one of the most rock-solid games out there, but everything broke in half when they found a use-after-free exploit in the game. They then figured out how to get arbitrary code execution and made the any% world record fall below 5 minutes. It's a glorious explanation of why use-after-free bugs are a problem. Really do watch the Retro Game Mechanics Explained video on how it works. It's a great watch.
It was a great talk and I got to talk with one of the speakers in the furry village afterwards. I'm glad I got to see it.
Domain Fronting Through Microsoft Azure and CloudFlare: How to Identify Viable Domain Fronting Proxies
Domain fronting is one of my favorite bug classes to consider. It's a classic time-of-check vs time-of-use bug where you have your SNI header claim you want to connect to one domain but then go and make your HTTP host header claim you want to connect to another. This is one of the tricks used to bypass nation-state firewalls like the Great Firewall, and it's a really neat trick. You basically put a postcard inside an envelope.
Somehow this technique is best documented on YouTube of all places. It's not really talked about in too much detail and CDN providers are usually quick to lock it down because it is a threat to their continued operation in countries that really want to filter internet traffic.
The basic threat model here is that if Cloudflare proxies like 20% of the Internet, that is critical mass enough that they can't just go and block Cloudflare without impeding the bread and circuses pipeline that their citizens rely on for entertainment. This is why people do domain fronting, it allows them to connect to websites that are simply blocked.
I have a friend that has been trying to help people inside Iran get free/open access to the Internet after they had some regime change recently. Domain fronting is one of/the main tool that they use because it's the only thing that's effective when government state actors block things like WireGuard and OpenVPN. He laments when big providers block domain fronting and are very reluctant to even acknowledge that it's a useful tool for people affected by extremist regimes and their censorship. I don't know of a good solution here.
Attacking Decentralized Identity
I admit, the well has been poisoned for me with regards to decentralized identity. I personally think that the problem is so intractable that it's probably a better use of our limited time on Earth to do something else and just farm it out to the usual suspects (or Tailscale!).
Going into it, I had read the Decentralized IDentifier (DID) spec and the DID Specification Registry method list that included a bunch of methods named after cryptocurrency projects. This really poisoned the well for me and I came into that talk thinking that it was some anuscoin shit that was thinly veiled as generic enough to pass muster to normal people.
I was wrong. It's actually a much lower level fundamental change to how we trust and validate identity in general. The basic idea is that the first model of identity on the internet was per-community and isolated to that community. The second model was logging in to bigger services to prove your identity and having those services vouch for you. This new third model essentially is having you vouch for yourself using public key cryptography.
It reeks of W3C disease including the use of JSON-LD for interchange and the acroynm is horrible. This technology is also so new that it hasn't even gotten close to stabilizing yet. I'm going to wait until it gets more mature before I try and use it.
Conclusion
Overall, I had a great time. I got exposed to things I never would have seen at home. I got to talk and dine with people that have only been words on a screen to me. I got to walk 50 kilometers around Vegas and take some great pictures of the city. I'm gonna do it again next year if I can. Maybe I can drag my husband along with me.
Introducing nixexpr: Nix expressions for JavaScript

As a regular reminder, it is a bad idea to give me ideas. Today's bad idea is brought to you by managerial nerd sniping, insomnia, and the letter "Q".
At a high level: writing complicated data structures in JavaScript kinda sucks. Here's an example of the kinds of things that I've been writing as I go down the ElasticSearch tour-de-insanite:
{
highlight: {
pre_tags: ['<em>'],
post_tags: ['</em>'],
require_field_match: false,
fields: {
body_content: {
fragment_size: 200,
number_of_fragments: 1,
},
},
},
}
This works, this is perfectly valid code. It creates an object that has a few nested layers of stuff in it, but overall I just don't like how it looks. I think it looks superfluous. What if we could make it look a little bit nicer? How about something like this?
{
highlight = {
pre_tags = [ "em" ];
post_tags = [ "</em>" ];
require_fields_match = false;
fields.body_content.fragment_size = 200;
fields.body_content.number_of_fragments = 1;
};
}
This is a Nix expression. It's a data structure that looks like JSON, but you have the power of a programming language at your fingertips. Note the difference between these two parts:
{
fields: {
body_content: {
fragment_size: 200,
number_of_fragments: 1,
},
},
}
{
fields.body_content.fragment_size = 200;
fields.body_content.number_of_fragments = 1;
}
These are semantically equal, but you don't have to use so much indentation and layering. These settings are all related, so it makes sense that the way that you use them is on the same level as the way that you define them.
If you want to try out this awesome power for yourself,
Install Nix and then add
@xeserv/nixexpr to your JavaScript dependencies.
npm install --save @xeserv/nixexpr
Then you can use it like this:
import { nix } from "@xeserv/nixexpr";
const someValue = "this is a string";
const myData = nix`{
hello = "world";
someValue = ${someValue};
}`;
console.log(myData);
I originally wrote this in Go for my scripting automation tool named yeet, but I think it's generically useful enough to exist in its own right in JavaScript. I think that there's a lot of things that the JavaScript ecosystem can gain from Nix, and I'm excited to see what people do with this.
This was made so I could write scripts like this:
// snipped for brevity
const url = slug.push("within.website");
const hash = nix.hashURL(url);
const expr = nix.expr`{ stdenv }:
stdenv.mkDerivation {
name = "within.website";
src = builtins.fetchurl {
url = ${url};
sha256 = ${hash};
};
phases = "installPhase";
installPhase = ''
tar xf $src
mkdir -p $out/bin
cp web $out/bin/withinwebsite
cp config.ts $out/config.ts
'';
}
`;
And then I'd be able to put that Nix expression into a file. I'll get into more details about this in a future post.

How it works
This is a very cheeky library, and it's all powered by one of the most fun to abuse Nix functions ever: builtins.fromJSON. This function takes a string and turns it into a Nix value at the interpreter level and it's part of the callpath for turning a string into an integer in Nix. It's an amazingly powerful function in its own right, but it gets even more fun when we bring JavaScript into the mix.
Any JavaScript data value (simple objects, strings, numbers, etc) can be
formatted as JSON with the JSON.stringify function:
> JSON.stringify({"hi": "there"})
'{"hi":"there"}'
This includes strings. So if we use JSON.stringify to convert it to a JSON
string, then string encode it again, we can inject arbitrary JavaScript code
into Nix expressions:
let formattedValue = `(builtins.fromJSON ${
JSON.stringify(JSON.stringify(value))
})`;
The most horrifying part about this hack is that it works.
What's next?
If this ends up getting used, I may try and make "fast paths" for strings and numbers so that they don't have to go through the JSON encoding/decoding process. But so far this works well enough for my purposes.
Introducing nixexpr: Nix expressions for JavaScript
CVE-2023-36325: Attackers can de-anonymize i2p hidden services with a message replay attack
tl;dr: If you host eepsites with Java i2p and are running older than i2p 2.3.0, update it as soon as possible. More details below.

A sufficiently determined attacker may be able to de-anonymize the public IPv4 and IPv6 addresses of i2p hidden services (eepsites) by using a combination of brute-forcing the entire i2p router set with a replayed message. This is CVE-2023-36325.
This issue was originally discovered by a user with the identifier
hbapm6le75xwc342hnkltwfnnmt4ccafr5wyf7b6jhw6jxn3fwqa.b32.i2p, which
I will refer to as "hbapm6". While hbapm6 was working on a custom
version of i2p, they found that replaying messages sent down client
tunnels to target i2p routers could cause the i2p software to drop the
packet instead of sending a "wrong destination" response. This can
lead to de-anonymization of a given eepsite by being able to correlate
the public IPv4 or IPv6 address of the contacted router with packets
being dropped.
This is fixed in i2p 2.3.0 by adding a unique identifier to every message ID and separating out bloom filters and other datastores so that such correlation attacks are harder to pull off in the future. These changes are protocol-compatible and all users are encouraged to apply them as soon as possible.
There is insufficent data as to what versions of i2p are vulnerable, but we are certain that 2.2.1 is vulnerable. It is likely that older versions of i2p are also vulnerable. Assume so.
This attack takes days to complete and requires a fairly detailed amount of knowledge of the i2p protocol in order to successfully de-anonymize target eepsites.
Users of i2pd are not affected.
With this understood, here is the CVSS score breakdown for this attack:
| Overall CVSS Score | 3.4 |
|---|---|
| CVSS Base Score | 5.3 |
| Impact Subscore | 1.4 |
| Exploitability Subscore | 3.9 |
| CVSS Temporal Score | 4.8 |
| CVSS Environmental Score | 3.4 |
| Modified Impact Subscore | 1.4 |
AV:N/AC:L/PR:N/UI:N/S:U/C:L/I:N/A:N/E:P/RL:O/RC:C/CR:M/IR:X/AR:X/MAV:N/MAC:H/MPR:N/MUI:N/MS:U/MC:L/MI:N/MA:N
Affected users should update to i2p 2.3.0 as soon as it is available.
The vulnerability has been mitigated by a refactor of the relevant codepaths involved with message parsing. Additionally, the network information database was sharded off with the hope of preventing future attacks.
On a side note, I have been very impressed with the i2p projects handling of the circumstances surrounding hbapm6 of the issues tracked as CVE-2023-36325. For an unknown reason, hbapm6 decided that the best way to get attention for these issues was to impersonate me. I was contacted by the i2p project due to hbapm6 acting very strange (IE: claiming to have a vuln and refusing to show proof of it or how they triggered it, if you have a de-anonymization attack for such a network, just share your code and demonstrate it when asked, it will save so much time for everyone involved), and after a month or two of cajoling, hbapm6 eventually managed to de-anonymize a throwaway VPS that was acting as an i2p router. This confirmed the vuln and lead to me filing this CVE.
I guess this is part of my threat profile now. Fun.
At the very least I got to have a conversation that was like (names have been changed to protect the innocent):
(hbapm6); Why all the snooping? [...] What is this, a game of Among Us?
(Me) <link to my website to an ascii art of an amogus with proof that I am the actual Xe Iaso>
I still have no idea why that person impersonated me. If you're out there and reading this and I wronged you somehow, I'm sorry and would like to know what I fucked up so I can change for the better.
There's some other vulnerabilities that are related to this, but none of them have viable attacks. Most of the changes being done are just various hardening to the pokey edges of the network database and other things. I expect that these are fairly minor issues and when the patch comes out you should probably update.
How to run a sysdiagnose on an iPad
Sometimes you need to dump your system logs for a developer of an application to understand why things are failing. sysdiagnose lets you have your iDevice emit a giant tarball of information so that they can pick out what the problem is.
However, their official button pressing procedure is finicky and doesn't give confirmation that anything is happening. Here's how you unconditionally force your iPad to do a sysdiagnose:
- Remove your iPad from the keyboard dock
- Disable Stage Manager
- Open Settings
- Tap Accessibility
- Tap Touch
- Tap AssistiveTouch
- Enable it
- Tap Customize Top Level Menu
- Add another icon
- Tap the empty icon
- Choose Analytics
- Swipe up to the home screen
- Tap the AssistiveTouch button
- Tap Analytics
- Wait for it to finish
- Open Settings
- Tap Privacy & Security
- Tap Analytics & Improvements
- Tap Analytics Data
- Scroll all the way to the bottom
- Find something called "sysdiagnose" and tap on it
- Tap the share icon in the upper right hand corner of the screen
- Save to Files
- Save to your iCloud Desktop folder
Then you can give the developer the file they need to diagnose the issue. Hope this helps!